What happened to the crypto scammers who stole ₿119,754 ($4.5 billion in today's prices) from Bitfinex?

Cryptocurrencies provide their users with super anonymity, something that scammers the world over use to their advantage. In actuality, the majority of networks (Bitcoin included) store full transaction history. This enables investigators to unravel even the most labyrinthine of trails from among thousands of transactions and dozens of user records.
It was recently revealed that US authorities had arrested couple Heather Morgan and Ilya Lichtenstein on charges of fraud, money laundering of illegally gotten funds and crimes against the United States. The Department of Justice has already made the biggest bust in its history, seizing coins worth ₿94,000 ($3.6 billion in today's price) stolen in the Bitfinex heist.
The Bitfinex robbery took place in 2016 and involved 2000 transactions to an external wallet with the ID 1CGA4s5.... Hackers were able to walk away with ₿119,754, which was worth $71 million at the time. In a bid to hide their tracks and cash in the coins, over the ensuing years, the fraudsters created numerous accounts on the darknet site AlphaBay and several accounts on various crypto exchanges using made-up names or false identities.
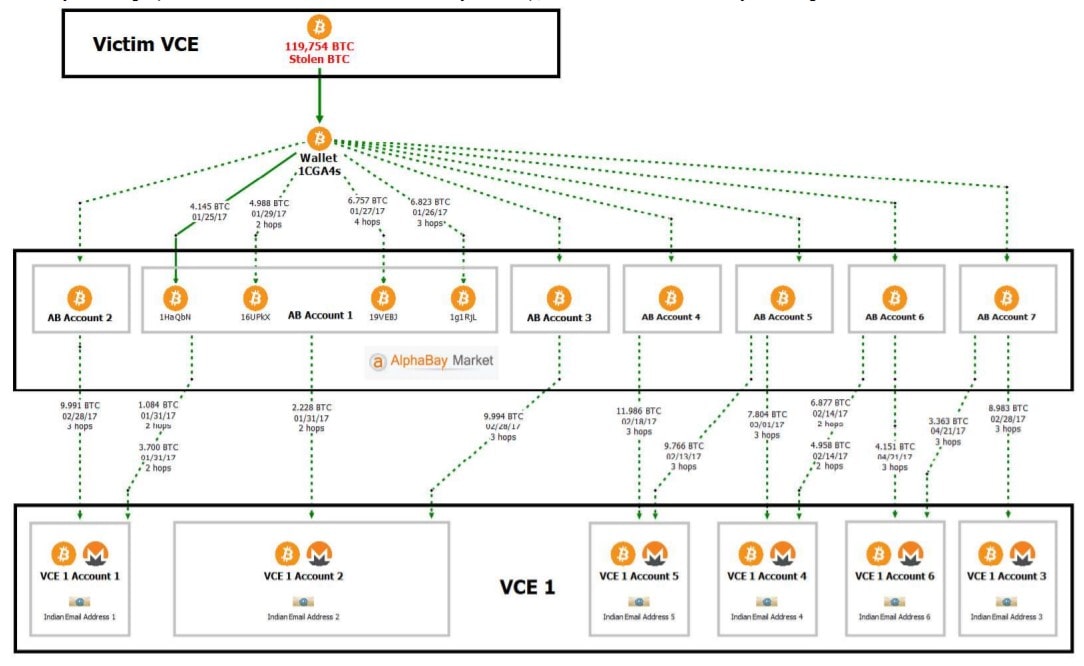
To hide their transaction history, Lichtenstein and Morgan made transactions from one account to another, often favouring coins with higher levels of anonymity, such as Monero. However, as is usually the case, they left crumbs of evidence here and there. For example, when creating accounts on one crypto exchange (VCE1), the scammers used similar e-mail addresses hosted with providers based in India. After being asked for additional documentation by the exchanges, Lichtenstein and Morgan went silent, which led to 18 accounts with total funds of $186,000 being frozen.
The stylistic similarity of the different accounts enabled investigators to go over the chain of transactions one by one until they established a link. Several of these were transferred to accounts opened in 2015 under the name of LICHTENSTEIN on a US-based cryptocurrency exchange (VCE5).
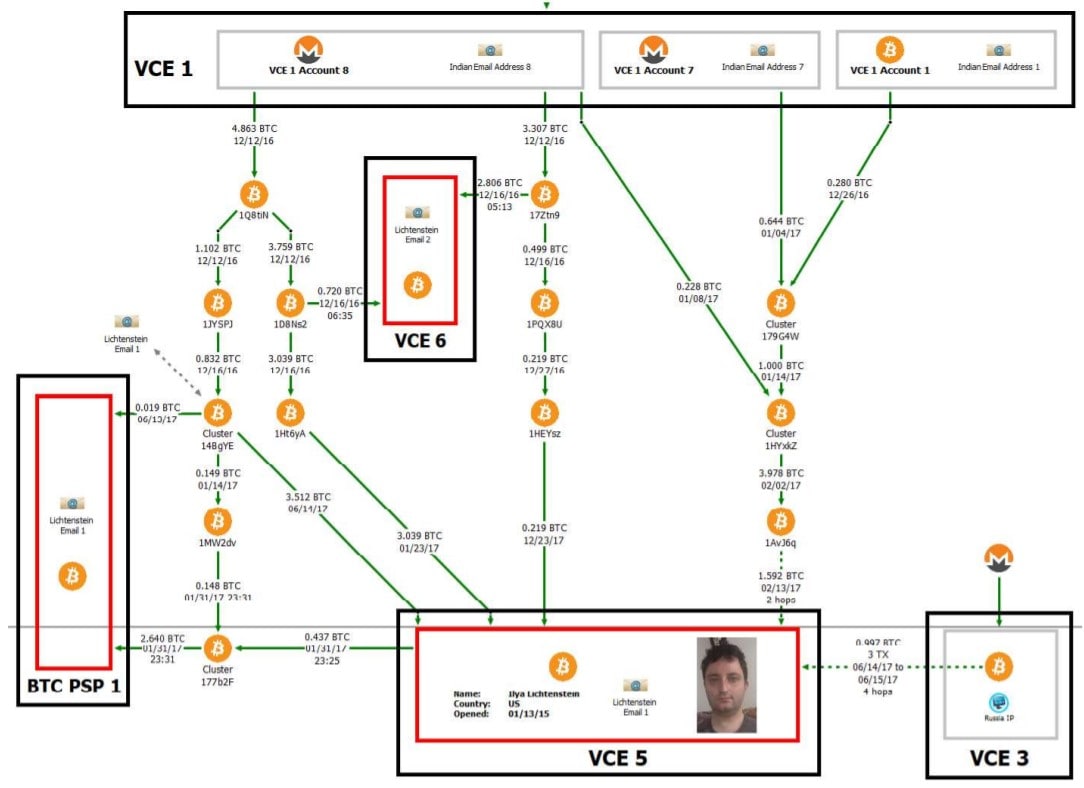
Since Lichtenstein used his driver's license to open accounts on the US crypto exchange, investigators were able to ascertain the suspect's identity along with other profiles and accounts in the United States. It emerged that Lichtenstein had created a fictitious company named SalesFolk that had been allegedly accepting cryptocurrency as payment for the provision of services. Further analysis of the transactions confirmed a direct link between the funds stolen from Bitfinex, which had flowed through an elaborate chain into Lichtenstein and Morgan's bank accounts.
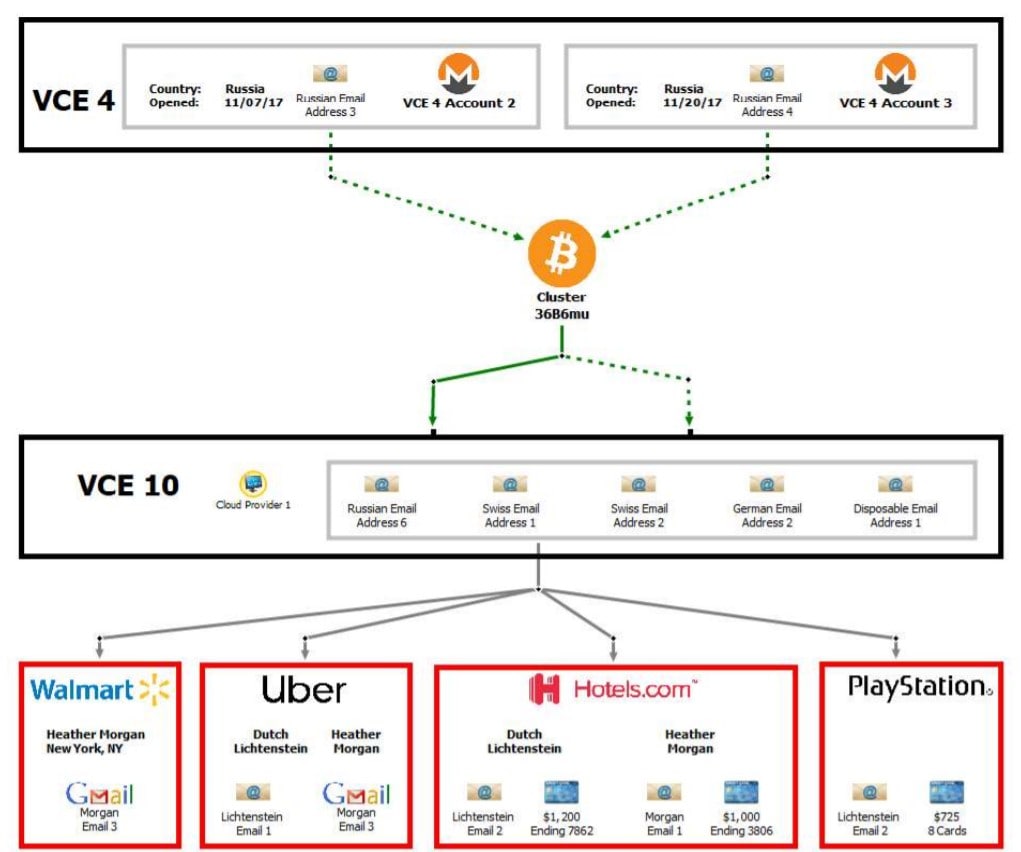
At one time, the fraudsters started to believe they were invulnerable and started using Cluster 3686mu to make purchases with cryptocurrencies, cutting the chain short in the process. For instance, on 3 May 2020, a Walmart gift card worth $500 was purchased using the account. The IP address used was altered, but security services sent a request to the cloud provider to reveal the owner and their e-mail address, which led directly back to Lichtenstein. A new iPhone was also purchased and delivered to the couple's home address.
Once sufficient evidence had been gathered against the couple, the security services secured a search warrant against the network provider and requested copies of all personal documentation held on the cloud. After the encrypted files were deciphered, investigators received access to all the crypto addresses in the chain, as well as their respective private keys. This enabled law enforcement to withdraw the entire remaining funds to DoJ-held accounts without the fraudsters' knowledge.
As it stands, the evidence collected is insufficient to prosecute the duo for the Bitfinex heist, but investigators are hoping to secure a plea deal in light of the 20-year prison term that Lichtenstein and Morgan face on the other charges.
StormGain analytical group
(cryptocurrency trading, exchange and storage platform)
Tags
Try our Bitcoin Cloud Miner and get additional crypto rewards based on your trading volume. It's immediately available upon registration.
Try our Bitcoin Cloud Miner and get additional crypto rewards based on your trading volume. It's immediately available upon registration.



