How Safe is Cryptocurrency Trading?

The popularity of mining, investing and trading cryptocurrencies is on the rise. However, there are many pitfalls — not just in cryptocurrency trading itself but also in storing and choosing which crypto to invest in. Is crypto trading safe? Every beginner attempting to get started in the cryptocurrency world asks themselves, "How safe is cryptocurrency trading, and what crypto trading risks are involved?" In this article, we decided to collect all available security-related information about cryptocurrencies so that anyone interested in the subject can minimise their risks.
Regardless of what experts say, it's still difficult to predict what awaits cryptocurrencies in the long term. Will they replace traditional money or occupy a narrow specialised niche in the world economy? Is trading cryptocurrency safe? In brief, cryptocurrencies will gain popularity as a means of payment and a way to attract investment.
Is Blockchain Secure?
Before discussing the risk management in trading crypto, let's find out how secure blockchains are.
The basic monetary units of any cryptocurrency are computer code lines. The developers encrypt this code to manage cryptocurrency and protect it from counterfeiting. The code of each crypto is stored in multiple copies of the programmable digital registry, a blockchain that runs on hundreds and thousands of individual computers. The general name of cryptocurrency monetary units are tokens, and among the top most common cryptocurrencies are Bitcoin (with a capitalisation of over $200 billion at the time of writing), Ethereum ($40 billion), Ripple ($11 billion) and Bitcoin Cash ($4 billion).
Blockchain software is a sort of bank vault that stores the tokens themselves and a register of transactions. A blockchain is a series of records (blocks) containing data and links through which each block is linked to the previous one. It's a distributed software system, which means that exact copies of the blockchain software and its data are located on multiple computers connected through a peer-to-peer (P2P) network.
All computers in this network use a consensus algorithm to confirm the registration of verified transactions and to verify new blockchain transactions. In other words, to steal tokens or modify a distributed registry in another way, cybercriminals will have to infect hundreds of thousands of computers on the network at the same time. Decentralisation and blockchain encryption protect cryptocurrencies from hacking.
General Cryptocurrency Risks
What are the main risks associated with crypto? Is it safe to trade cryptocurrency? The risks associated with the lack of psychological discipline and management will not be discussed, as these skills depend entirely on the trader. Obtaining such skills is a long process, but the best book for cryptocurrency trading will speed up your path to success. To assess cyber risks, it's useful to understand which elements of cryptocurrencies are potential targets for hackers.

Miners and Malware
When a blockchain PC processes an encrypted transaction, it adds information about it to one of the blocks. As a reward for this transaction, the issuer — i.e., the one who issues the cryptographic currency — issues tokens to the PC owner. Processing transactions and receiving payment in the form of tokens is called 'mining'. However, this operation is not always legal. In illegal token mining, malware can use up to 65% of the CPU or video card power on the victim's computer.
Soon after the notorious WannaCry in May 2017, the Adylkuzz malware, which used a vulnerability called EternalBlue, became active. It succeeded in turning 200,000 computers into slave miners. The owners of the infected PCs paid for the processing power needed to perform blockchain transactions, while the fraudsters who managed the slave PCs earned money from mining. They received about one million euros in Monero cryptocurrency for free.
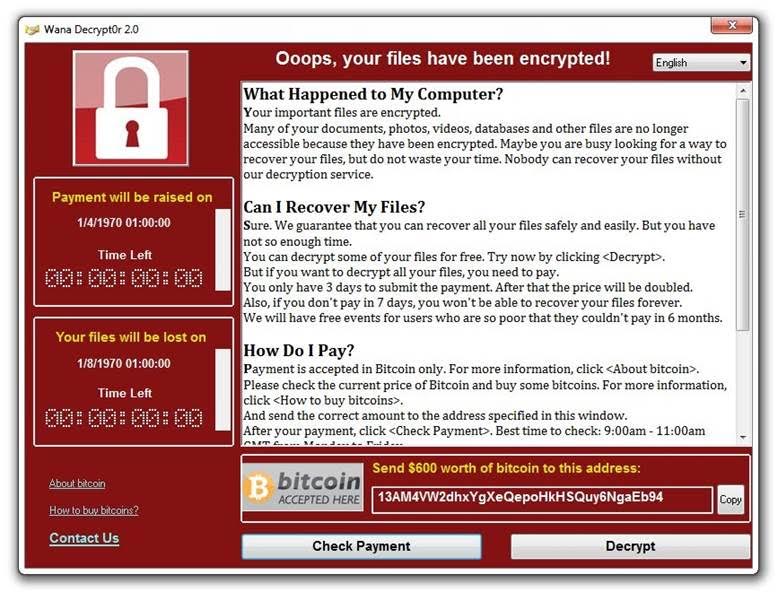
According to Check Point Threat Intelligence,for the period from July to December 2017, one in five companies was affected by illegal cryptocurrency mining. In December 2017, 55% of companies around the world were attacked by crypto miners. At the same time, 10 varieties of this malware hit the top 100 most active cyber threats. The most active was the CoinHive malware, which also uses its victims' PC power.
Attack on Crypto Exchanges
Cryptocurrency exchanges are websites where anyone can buy, sell or exchange cryptocurrencies. Despite security measures taken by exchanges, criminals are finding vulnerabilities. For example, in July 2017, criminals stole Bitcoin from customers of the world's fourth-largest exchange, Bithumb, located in South Korea, getting it listed among the high-risk crypto exchanges. To do this, they first stole the personal data of 31,000 users from a Bithumb employee's computer, and then used the information obtained to conduct an attack using social engineering. The scammers called the user database and tricked them into reporting their wallet data before stealing Bitcoin from their accounts.
The Kucoin exchange was the victim of the latest hack on 25 September 2020. The trading platform lost more than an estimated $200 million in cryptocurrency.
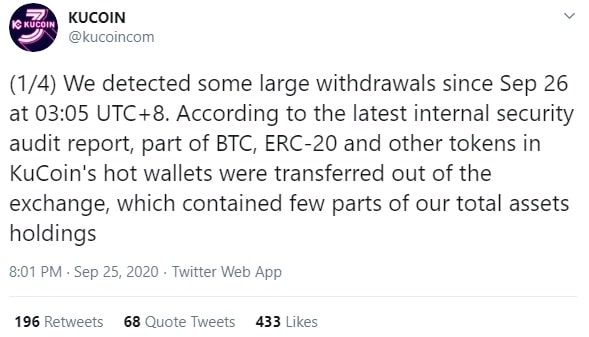
Cybercriminals can also conduct denial of service attacks to manipulate the value of crypto on the exchange. Since the price of Bitcoin is set by several exchanges around the world, blocking access to the websites of one or more exchanges will allow the trader involved in a scheme to earn on the difference in rates. In practice, hackers used DDoS attacks against two exchanges, Bitfinex and BTC-e, to manipulate the cost of the cryptocurrency.
Wallet Security
A cryptocurrency wallet is different from an electronic wallet: the latter stores digital versions of credit cards, bank cards and other standard payment methods, while the former is a software application that contains the owner's public and secret encryption keys. Users employ this software to communicate with the blockchain. Crypto wallets are used to make transactions and track tokens stored in the blockchain. The tokens themselves are not in the wallet. To learn more about how to use a crypto wallet, please read our blog.
Today, crypto wallets are as protected as their owners. The cryptocurrency wallet app installed on your computer or smartphone can be compromised if cybercriminals steal login data. To steal it, they can use malicious apps, spyware, phishing or other standard attack methods.
How to Safely Trade or Mine Cryptocurrencies
Like any new technology, there are certain risks of trading cryptocurrency. This is what you need to remember when it comes to choosing a safe crypto trading platform, blockchain and crypto security:
- Processing block transactions (mining) is an operation that brings good profit, so hacking a large number of computers can be a profitable business for hackers. This crypto trading risk is particularly high if the organisation uses scalable virtual machines in a poorly secured public cloud. Whether your IT programmes are running on the company network or on a public cloud, you need to secure your computing resources with advanced threat prevention and bot protection technologies so that your PC doesn't become a slave and you aren't forced to pay for tokens from others.
- Cryptocurrency miners must also install advanced threat prevention software on their computers to prevent the illegal use of computing resources, DDoS attacks, malware infections that collect information about computer operations or attempts to steal cryptocurrency. In addition, they must systematically test the software for vulnerabilities and malicious code. They should beware of the fundamental crypto trading rules. It's also important to ensure that all block network operators have recommended software updates and patches installed.
- Cryptocurrency exchanges need to protect their core networks from DDoS attacks and advanced threats. They also need to protect both their websites from hacking and data leaks and defend employee computers so that client data doesn't fall into the hands of criminals. StormGain is a time-tested, safe crypto trading platform with one of the industry's best security solutions and is constantly improving its security systems.
- Ordinary cryptocurrency users should be aware of their devices' security. Installing antivirus software on all devices they use to access their cryptocurrency wallet (including smartphones) is a must to protect against threats. Don't share wallet login information with anyone. The user is responsible for protecting this information from theft through spyware and/or phishing.
We hope that this article explained the main threats and crypto trading risks associated with storing and mining cryptocurrencies. Remember: the safety and security of your cryptocurrency and private data are your responsibility. We wish you good luck and safe crypto trading.
Tags
Try our Bitcoin Cloud Miner and get additional crypto rewards based on your trading volume. It's immediately available upon registration.
Try our Bitcoin Cloud Miner and get additional crypto rewards based on your trading volume. It's immediately available upon registration.
FAQ
Why is cryptocurrency high-risk? Or not?
Trading is a high-risk decision in most cases. The decision to invest in cryptocurrency carries inherent crypto trading risks. Financial institutions must safeguard against fraud and money laundering, potentially making investors vulnerable to such activities. Unlike traditional fraud victims, those affected by crypto fraud may not have the same legal protections due to the decentralised nature of cryptocurrency.
Is trading crypto safe?
Cryptocurrency investment carries high crypto trading risks compared to stocks and government bonds due to its volatility and uncertain regulations. While legal in Europe, cryptocurrency remains largely unregulated and susceptible to changing rules. For instance, China's crackdown on crypto in 2021 led to a significant drop in Bitcoin's value, highlighting the market's vulnerability. Additionally, the newness of cryptocurrency means investors are still navigating its behaviour, leading to significant price fluctuations driven by market sentiment. Even established cryptocurrencies like Bitcoin are known for their drastic price swings.
Is high trading volume good or bad?
The significance of high trading volume can be a topic of debate. When a stock shows an increase in value accompanied by high trading volume, it is generally considered a more sustainable trend. Conversely, if a stock's value rises with low trading volume, it could indicate a temporary increase known as a "dead cat bounce." The higher trading volume suggests increased demand for a stock, influencing its price.
Is crypto trading safe?
Investing in cryptocurrency is considered to be highly risky. There are numerous risks of trading cryptocurrency, but one of the main reasons it's not a secure investment is its potential for massive price fluctuations in a short period. This rapid fluctuation in price is referred to as volatility in the investment world, and it's generally unfavourable for an investment portfolio.
Is crypto safer than stocks?
Cryptocurrencies are often viewed as riskier than stocks because of their high volatility, limited regulatory oversight, and relative newness. Although stocks are generally more stable, they are still susceptible to risks of trading cryptocurrency, such as market downturns and company-specific issues.



